When Encryption Fails Before It Begins
In early April 2026, WhatsApp revealed it had quietly disrupted a targeted spyware campaign affecting around 200 users most of them in Italy. At first glance, the number seems small. But the method used and the company behind it signals a deeper vulnerability in how modern surveillance operates.
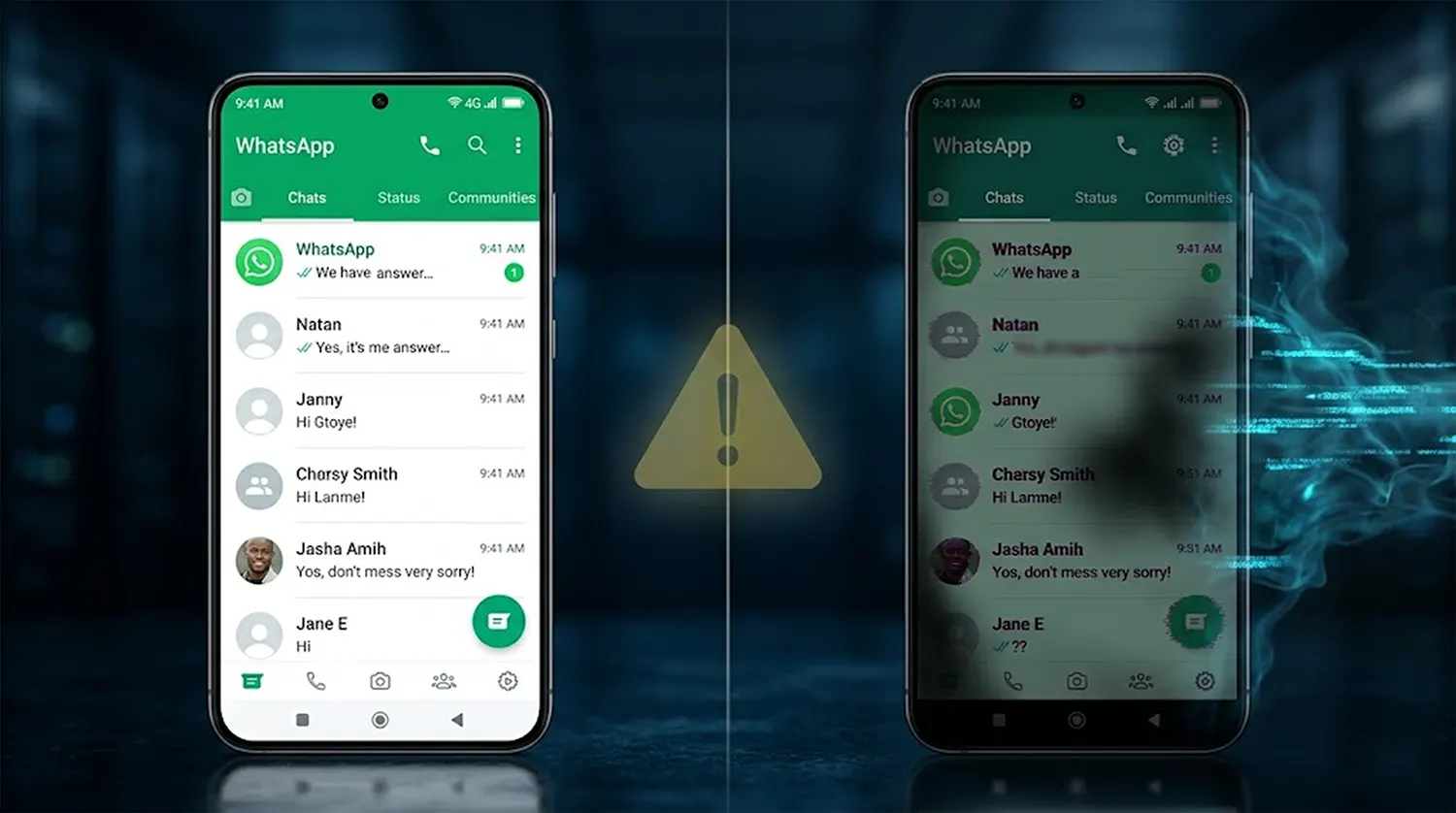
The attack did not break encryption. It didn’t need to. Instead, victims were tricked into downloading a counterfeit version of WhatsApp, effectively bypassing security before it even had a chance to work. In other words, the system wasn’t hacked; the user was.
Behind the operation was ASIGINT, a subsidiary of the Italian firm SIO S.p.A., now increasingly described as part of the “mercenary spyware” industry, a shadowy sector selling surveillance tools to governments under the banner of law enforcement.
The Rise of “Mercenary Spyware” Moves Into Plain Sight
ASIGINT is not an anomaly. It represents a growing class of companies that build tools designed to infiltrate encrypted platforms like WhatsApp or Signal. These firms operate in a legal gray zone: they market themselves as partners to governments, but their tools often mirror the capabilities of state grade cyber weapons.
Their business model is straightforward. Governments outsource surveillance. Companies like ASIGINT provide the tools. Accountability becomes diffuse.
The spyware linked to this campaign known among researchers as “Spyrtacus” is particularly invasive. Once installed, it can:
- Extract messages and chat histories
- Access call logs and contacts
- Track GPS location
- Activate microphones and cameras without user awareness
This level of access effectively turns a smartphone into a live surveillance device.
What makes this case unusual, however, is not just the capability but the delivery mechanism.
The Loophole That Swallowed the Lock
Unlike previous high profile spyware attacks that relied on “zero day” vulnerabilities
hidden flaws in software, this campaign used social engineering. Victims were sent convincing messages prompting them to install what appeared to be a legitimate or beta version of WhatsApp.
That distinction matters. A zero day exploit is a technical failure. This was a psychological one.
By persuading users to step outside the controlled ecosystem of official app stores, the attackers rendered WhatsApp’s end to end encryption irrelevant. The fake app functioned as a “dummy client,” capturing data before it could ever be encrypted.
Encryption, in this context, becomes a locked door installed inside a compromised building.
This shift from breaking systems to manipulating users reflects a broader trend in cyber operations. As platforms harden their infrastructure, attackers increasingly target human behavior as the weakest link.
Meta’s Legal Strategy Is Becoming a Deterrence Doctrine
WhatsApp’s response was both swift and unusually aggressive. The company remotely logged out all affected users, issued direct warnings, and blocked the infrastructure linked to the spyware campaign.
But the more consequential move came on the legal front.
Meta, WhatsApp’s parent company, issued a formal cease and desist demand to ASIGINT and SIO. This is not just damage control, it is part of a broader strategy to dismantle the spyware for hire ecosystem through litigation.
That strategy gained credibility in May 2025, when a U.S. jury ordered the Israeli firm NSO Group to pay Meta $167 million in damages. The ruling established a critical precedent: companies cannot hide behind government contracts to justify hacking private platforms.
By invoking that case, Meta is sending a clear message. These firms are no longer treated as legitimate vendors. They are being reframed as legal liabilities.
If pursued, a lawsuit against ASIGINT could further solidify this emerging doctrine, one where courts, rather than regulators, become the primary battleground.
Italy’s Domestic Surveillance Debate Reignites
The fact that this case centers on an Italian firm adds a layer of political sensitivity. Italy has already faced scrutiny over its surveillance practices following a separate spyware scandal in 2025.
Now, the revelation that a domestic company linked to law enforcement partnerships
used deceptive tactics against users has reignited debate in Rome.
The core question is no longer whether surveillance tools should exist, but how they are deployed and against whom.
If companies operating within national jurisdictions are targeting their own citizens using covert methods, the line between lawful surveillance and abuse becomes increasingly blurred.
This has placed Italy’s Interior Ministry under pressure to clarify oversight mechanisms, procurement standards, and the legal boundaries governing such tools.
The Illusion of Safety in Encrypted Platforms
For years, encrypted messaging apps have marketed themselves as the gold standard for digital privacy. And technically, that claim still holds. WhatsApp confirmed that its core encryption was never compromised.
Yet this incident underscores a more uncomfortable reality.
Security is no longer defined solely by cryptography, it is defined by the entire ecosystem surrounding it.
If users can be tricked into installing a counterfeit version of an app, encryption offers no protection. The data is exposed before it ever enters the secure channel.
This reframes the debate. The question is no longer “Is encryption strong enough?” but rather:
Can users reliably distinguish between what is real and what is not?
A Market That Thrives in the Shadows
The spyware for hire industry continues to expand because it serves a persistent demand. Governments need intelligence capabilities. Building them internally is expensive and slow. Outsourcing is faster and politically convenient.
But as this case illustrates, outsourcing surveillance also outsources risk.
When private firms operate with limited transparency, the potential for misuse grows. And when those firms are exposed, the fallout extends beyond the company itself touching governments, legal systems, and public trust.
Meta’s legal campaign is an attempt to disrupt this market from the outside. Whether it succeeds will depend not only on court rulings, but on whether governments themselves are willing to impose stricter controls on the tools they procure.
The Real Vulnerability Isn’t Technical
The takeaway from this episode is deceptively simple.
Even the most secure system can be undone by a single act of deception.
No exploit was needed. No encryption was broken. The attack worked because it convinced users to step outside the boundaries of trusted software.
And that may be the most difficult vulnerability to fix.
Because unlike code, human judgment cannot be patched.